Why It’s Time to Invest in
It seems like we hear about new cyber security breaches every single day. We constantly hear about large breaches like Adobe, Equifax, or a city government. In addition, thousands of smaller companies become victims of cyber-attacks every year.
With the number of successful attacks and the wide range of stolen data being sold on the dark web and through other sources, it can seem like there’s nothing to be done to protect yourself. Clever hackers, the thought goes, will eventually break through any firewall, server or connected device.
But the truth is, you can protect your organization from the vast majority of attacks. In fact, most victims – even the notorious ones such as Equifax – could have stopped or reduced the damage if they had taken a more complete approach to cyber security.
Your assumption might be correct. Smart cyber criminals probably can get to you even if you do have a strong cyber security program. But most cyber criminals aren’t that smart. They are just opportunists who go around looking for easy targets.
That’s why it’s time for every organization to take the time and money required to invest in cyber security services. It’s how you go from being an easy target to being able to protect yourself.
Why Cyber Security Services Are Essential
The challenge of protecting your organization from cyber-attacks is three-fold:
- You must increase the security of your network.
- You must stay up to date on every new attack risk and create a plan to manage that risk.
- Your employees must stay vigilant and aware of the best ways to protect your organization.
If you have a robust technology investment and a technically minded staff, you may be able to do the work of hardening your servers and software from an attack. You may also be able to spend the time to stay updated on the latest threats. But employee training is a different challenge altogether.
On the other side of the coin, an organization with a strong employee development program may have top-notch employee training but have less expertise with technology.
Handling these three major jobs internally is too much even for larger organizations. So, they will often turn to outside vendors to provide one or all of these services.
Your Data is More Valuable Than Ever
One of the main reasons that cyber-crime is on the rise is that organizations are generating more and more value from the data they collect and process. It’s not just about stealing credit card numbers and using them to make purchases. The actual data itself is so valuable that it can be sold or held ransom by anyone with access to it.
Generation or collection of data from customers, logistics, or in the field has fueled all of the recent major advancements in business technology. From the serving of ads to tracking groceries from farm to table, it’s all about the data.
Data-driven applications are projected to account for $13 trillion in business in the next 10 years. That kind of investment and the creation of that kind of value means that data is worth big money and must be protected, like any investment.
Tightening up the gaps
The majority of successful cyber attacks use known vulnerabilities in software that have already been addressed by the vendor. This means that the method of configuring or patching – modifying – the software to remove the vulnerability was already available. But the victim of the attack had not yet implemented it.
There are several reasons why software and firmware goes unpatched and leaves an organization open to a cyber-attack. These types of vulnerabilities can happen anywhere, including servers, cloud applications, desktops, laptops, routers, switches — even your smart refrigerator. That leaves a lot to keep track of and in many cases the responsible party already has other job duties beyond keeping up to date on security. So, this person might not become aware of every single patch and update in a timely manner.
Depending on the application and how much it’s used on your network, patching can be an extremely time-consuming manual process. The same goes for changing the configuration to close vulnerable ports or other entry points. Many organizations might not have enough resources to make regular deployments of new software and firmware updates.
The specific dependencies of an application might also not allow patching or updating to a newer version. If you have an application that needs a specific version of an operating system to run, then you may not be able to immediately make the OS patch until a complementary patch is available for the application.
You might also not be able to afford the downtime required to perform a large-scale update to the network or may lack the time to do a full test on the interaction between a new patch and every single application. There can also be a tendency among users to not want to upgrade from a known version that they were comfortable with.
Those are the common excuses that typical organizations have for not applying patches. This is one reason why bringing in a cyber security service have help navigate the complicated process of closing the gaps in your system.
Stopping Social Engineering
In addition to the technical holes in your network environment, cybercriminals also look to exploit people. Using people to bypass normal security is known as social engineering. It takes many forms, but the common factor is that your employees are tricked into opening up the doors to your systems or (sometimes literally) to your buildings.
Cybercriminals engaging in social engineering try to take advantage of people’s genuine willingness to help – particularly in a customer-service focused environment. Most people are taught to be open and helpful, avoiding “no” in response to a customer request. It goes against most business training to be openly suspicious of someone who appears to be a vendor, fellow employee or customer.
Social engineering comes in several forms:
- Piggybacking or tailgating:
They simply follow an employee through a door with an access code or card. Attackers may pretend to be an employee who forgot their card or will simply count on the fact that most people aren’t interested in being confrontational around the office. - Baiting:
An attacker might leave a USB key infested with malware in a place that one of your employees might find it. As soon as they plug it in, it infects your system. - Impersonation:
An attacker might arrive at your facility in the uniform of a technician from a local utility. They request access to your network closet to do some urgent work. An unaware individual is likely to let them in, giving them a way to directly connect to your systems. - Watering hole:
If an attacker can control a trusted site that you visit often, they can capture credentials and access to your private data. - Phishing:
Fake emails take many forms. The successful ones generally request urgent action. They may impersonate a financial officer in the company and request an immediate transfer of emergency funds. A quick-acting employee may respond to the request before confirming it or thinking it through. Again, the attacker is taking advantage of people’s genuine trust and desire to do something good. - Spear phishing:
This type of attack targets a specific individual. By accessing public social media accounts, the attackers learn details about a specific person that make their phishing attacks more convincing. They may know that the boss likes to play tennis. So, they send an email asking for urgent information to be sent before a tennis match with a big customer. The employee who sees this is likely to quickly send the information in order to make sure the boss can close the important deal.
The only way to prevent social engineering attacks is to have a vigilant staff. This requires the ability to communicate the importance of remaining vigilant, education in the form of on-going training, and some form of testing with simulated social engineering attempts. An in-depth and comprehensive program can be developed and managed in-house if you can afford dedicated resources, but this is an area where it may be too risky to ignore the chance to seek outside help.
Cyber Insurance
Organizations that are concerned about the risk of a data breach may look to buy a cyber insurance policy. These policies can help cover your liability if you are the target of the data breach. They will also pay to get you back up and running in the event of an attack on your systems.
There are a few different types of cyber insurance that cover different cases.
- Cyber Security: This insurance covers your costs associated with damage done directly to your business. It will cover not only the cost of getting your system running again, but also the hiring of forensic analysis experts to determine what happened, PR firms to cover loss of reputation, as well as the cost of notifying any customers or other owners of lost sensitive data.
- Cyber Liability: This insurance covers third-party costs you incur in the form of damages from lost data. This includes customers who had credit card numbers or other personal information compromised or any trade secrets or intellectual property belonging to one of your corporate partners.
- Technology Errors & Omissions: This covers the cost of defending you from a negligence claim for any electronic products or services you sell. This could include producing faulty code or deploying files that accidentally damage someone else’s system.
There are many other specific use cases for cyber insurance. But the one thing they have in common is that taking proactive efforts to secure your systems and develop best practices will lower your premiums and may be a requirement in order to buy cyber insurance.
How Cyber Security Services Help
Bringing in outside help for your cyber security requirements – either for complete solutions or help with certain areas – can save you time, money and a lot of worry.
Cyber Security is both a basic business requirement for everyone and an extremely complicated topic. The support of an outside vendor brings focus and special expertise where it’s needed as well as a different perspective on how you currently handle security.
Full IT Risk Assessment & Risk Management Plan
The first step that a cyber security service provider can help with is a full risk assessment. This is a process in which you examine your current cyber security plan and carefully analyze your risk factors in every area that affects your network.
The Risk Assessment starts by conducting a full inventory of IT assets. This includes servers, local devices, websites, connectivity, and – most importantly – your valuable data.
Then you identify potential attack vectors or other events that could cause a disruption in normal operations. This is basically a list of everything that can go wrong, from ransomware attacks to an earthquake hitting your data center.
With this you are able to assess the specific vulnerabilities that could impact your IT operations. This helps you understand the disruption each type of event can cause to your business.
After completing the above steps, you tie it all together with an analysis of the likelihood of each event actually happening. The potential damage combined with how likely something is to occur gives you a risk factor for each vulnerability.
Understanding and identifying every single risk is a big challenge on itself. The work is compounded when you need to research and understand not only the financial impact if an event happens, but also how likely it is to happen. This data can be researched online, but it takes an expert in the field of cyber security to pull it all together and create a complete IT risk assessment. When a cyber security service provider comes on board to help with your assessment, you will provide the knowledge of your systems and vital operations and they will use that information to create a complete picture of your specific risk factors.
With a full understanding of your risk factors, you can create a Risk Management Plan. This is a statement of the organization’s understanding of each risk factor and the steps taken to manage the risk. Some risk factors might be so high that they require immediate change to address. Others might be low enough that you can defer mitigation or accept the risk.
The Risk Assessment and Risk Management plans are typically revisited and updated annually. After the initial work, the annual reviews become much easier and straight-forward, provided you are aware of developments in new IT threats and vulnerabilities.
Creating a Policy
A Cyber Security policy is a statement of your organization’s response to the IT Risk Assessment. It identifies your specific response to the Risk Management Plan. Cyber Security Policies include rules to operate your IT systems, incorporate regulations that govern how you do business (such as national or local policies on IT data), and outline your company’s specific plans to enforce these rules or train your personnel to understand them.
While most Cyber Security Policies are pretty similar, yours should be customized to specifically address the threats and vulnerabilities that will impact you the most. This is another situation where an outside experienced service provider will have helpful insight into best practices that can be applied to your organization.
Deploying the Policy
Putting policies into effect will take time and effort. You might need to create a new position or reorganize your IT staff to effectively take care of any new policy elements you introduce. New policies may include creating and maintaining an inventory of current assets or taking responsibility for patches and upgrades. You also might begin a program of penetration testing or simulated phishing attacks to support your employee training.
As with much of this process, it is always possible to rely on internal personnel, but investing in a cyber security services provider may be easier and deliver more bang for the buck.
User Training
By far, the most important aspect of a new cyber security plan is to train your users. Increased security efforts are practically useless if you don’t have buy-in from your userbase. Getting everyone up to speed will take some time and could be a difficult process, but it will go a long way towards protecting your IT systems.
User training covers all aspects of your security policy, with a strong focus on helping users understand how their behavior can affect the overall security of the organization. User training can be conducted in instructor-led classes, by webinar, in a recorded environment, or in practical scenario-based testing such as phony phishing attempts.
Training topics should include the basics for everyone and job-specific training for certain individuals. Areas of general concern include:
- Workplace best practices:
How to maintain security in the building, clean desk policies, strong passwords and other office protocols. - Remote best practices:
How to secure your home network, how to stay safe on public networks such as airports, and how to secure laptops and mobile devices. Plus, you will be able to educate your employees on what to do if a company-owned device is lost or stolen. - Protecting customer information:
Understanding the impact of lost customer data, controlling access to customer data, and safely using customer data within organization guidelines. - Email, browsing and social media:
Understanding phishing, spam, safe web practices, and the proper use of social media in a workplace environment.
The role of a Cyber Security Services Provider
A good cyber security services company can do all of the above or provide specific guidance and materials to help you accomplish your goals. At minimum, the outside perspective and insight available from an impartial source is a valuable tool to make sure you have covered everything.
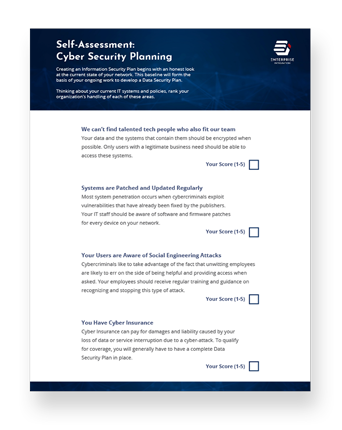
Cyber Security Checklist.